Our Clients and Network
Worldwide leader and provider for crash barriers and perimeter security fencing
Worldwide leader and provider for crash barriers and perimeter security fencing
Our Products

Latest News
Stay ahead of the curve in perimeter security and crash-rated barrier design.
Our News section features expert insights, real-world project experience, and the latest innovations in site protection.
Check out the featured post on the right to see what’s new in securing tomorrow’s facilities.
Portable Vehicle Barriers vs. Permanent Solutions: When Each One Is the Right Call
Compare portable vehicle barriers vs. permanent anti-ram systems. Learn which solution fits your threat environment, deployment needs, and budget.

What We Do
Black Security Products is committed to providing a wide range of services!
Solution/Design Engineering
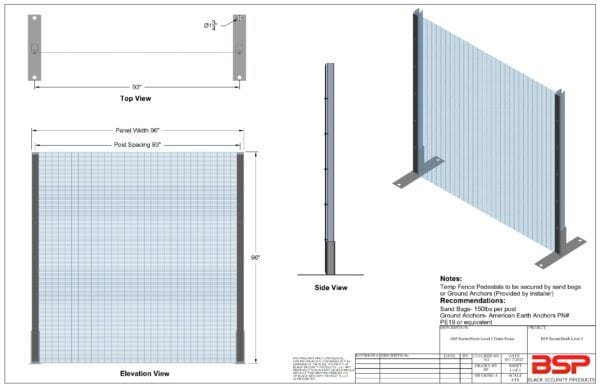
Many projects are remarkably simple and straight-forward, while others can be more complex and require customization. BSP offers full design support and has partnered with the largest A&E firms such as Atkins, Jacobs and Fluor.
Technical Approach
BSP’s technical approach is first to review and understand the site requirements and security assessment of the specific project. This allows us to “begin with the end in mind” to ensure overall project success on time and on budget.
Product Manufacturing
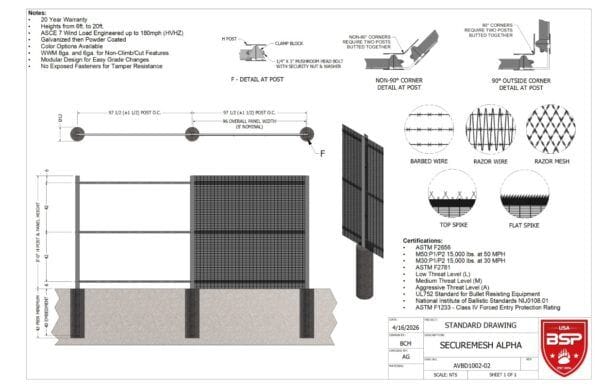
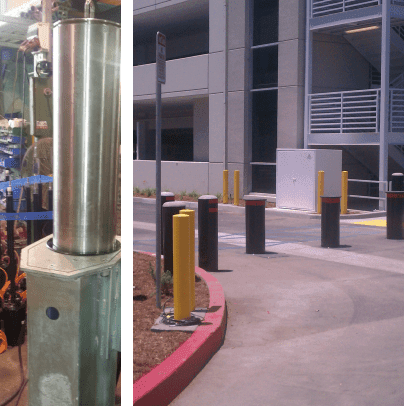
BSP proudly showcases products in the United States Department of Defense (DoD) Anti-Ram Vehicle Barrier List, which is a sample of the products that are designed and manufactured (in the US) by BSP to help actively protect important/high risk assets across the world.
Standards and Specifications
Standards and Specifications are part of our foundation at BSP, as our clients rely on standards from the US, UK and Europe. At BSP, we consider ourselves subject matter experts on the international testing standards to include ASTM International F2656; Publicly Available Specification (PAS) 68; and CEN Workshop Agreement (CWA) 16221.
Client Care
BSP has earned an impeccable reputation in the physical and perimeter security industries as we understand the importance of details, scope of work, threat assessments and specifications on our projects, regardless of size or technical magnitude. Our understanding allows us to provide unparalleled customer service throughout and after the project completion.
Research and Development
We proactively monitor the security industry as violent attacks continue to increase across the globe. We believe that it is imperative to stay ahead of the competition and threats, which is why we are focused on improving and designing new ways to protect your assets.

Partner with the Team You Can Trust
At Black Security Products, our team is the driving force behind every success, both ours and that of our clients.
With decades of combined experience in public safety and perimeter security, our professionals are dedicated to delivering reliable, cost-effective solutions tailored to real-world needs. It's this expertise, passion, and commitment to excellence that sets us apart and ensures every project we support is built on a foundation of trust and performance.

Cutting-edge solutions to safeguard what matters most.